Platform
A hosted authority runtime for autonomous agents.
The Intended platform is a hosted authority runtime backed by Large Intent Models, the Open Intent Layer taxonomy, and the Enterprise Capability Engine. Agents send intents to the Intended API. The runtime interprets, classifies, maps to your capability model, evaluates policy and risk, and — for approved actions — issues a signed Authority Decision Token. Every decision is recorded in a tamper-evident audit chain. Downstream systems verify the token before executing. No Token, No Action.
One interface. Two implementations.
The operator surface
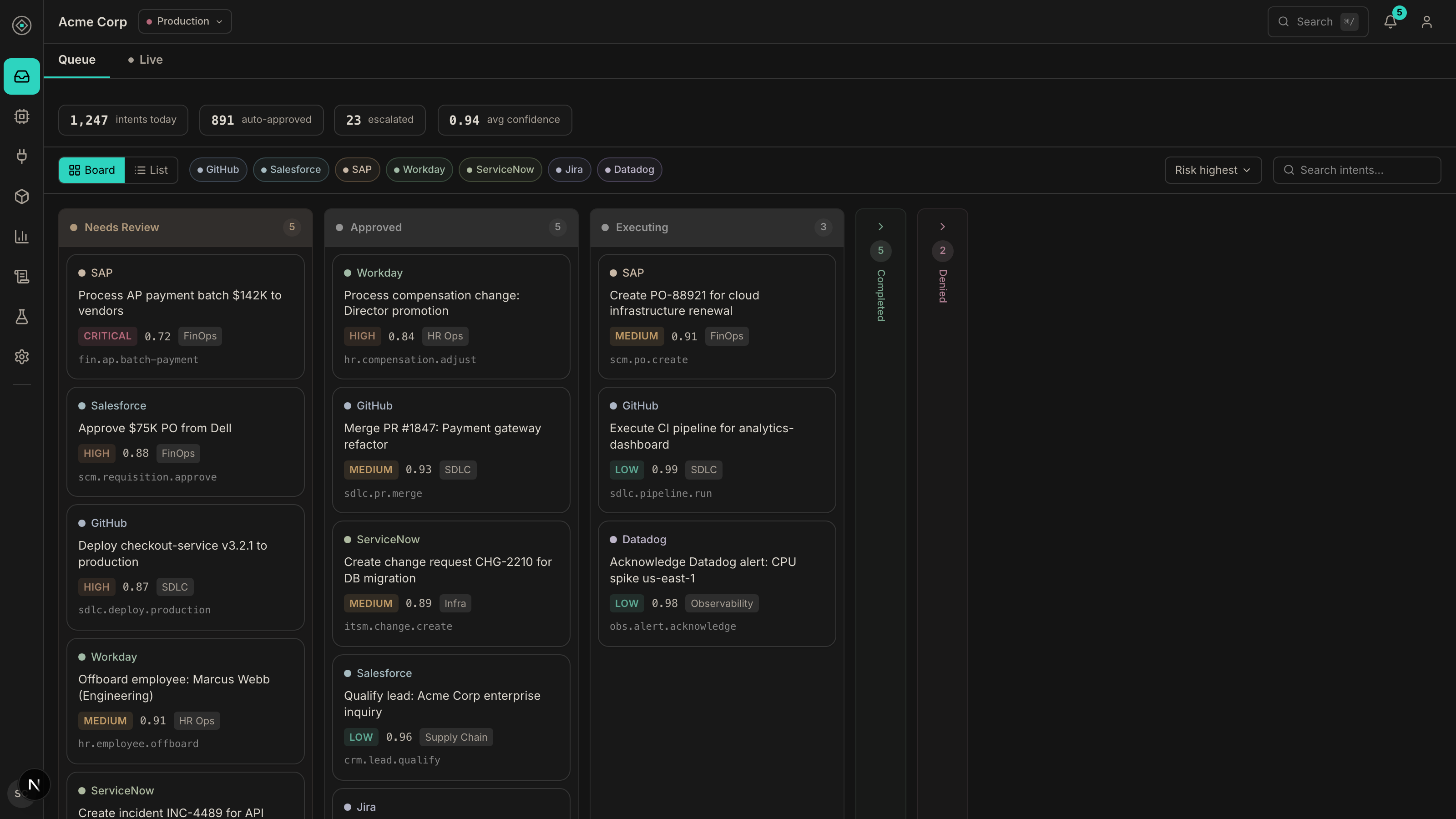
Every decision in one reviewable queue.
Operators land on a single decision queue that groups intents by state — needs review, approved, executing — with risk, confidence, and governed runtime context on every card. High-impact actions escalate to the right reviewer with full evidence attached.
How the platform works
From raw action to verified execution.
Define and interpret intent
Open Intent Layer classification and Large Intent Model interpretation make the action legible.
Structure and verify
The Intent Object is checked by the Enterprise Capability Engine against capability context.
Decide
The Authority Engine returns ALLOW, DENY, or ESCALATE using verified intent and policy.
Grant authority
Approved actions receive a cryptographic Authority Token with scope, TTL, and single-use semantics.
Execute and prove
Execution validates the token at the boundary and the result is recorded in the immutable audit chain.
Capabilities
Everything required to evaluate the system seriously.
Open Intent Layer
The shared, open language for defining what agent actions are intended to do across tools, runtimes, and enterprise systems.
Large Intent Model
Interprets the action in context so the platform understands what the agent means, not just what it called.
Intent Object
Structures intent into the representation that verification, replay, escalation, and audit all work from.
Enterprise Capability Engine
Verifies the Intent Object against enterprise capability boundaries and operational context.
Authority Engine
Evaluates policy against verified intent and returns ALLOW, DENY, or ESCALATE with a clear decision path.
Authority Tokens
Cryptographic proof that an action was verified as intended and is authorized to execute.
Escalation workflows
Route high-risk actions to the right approver with context, evidence, and attributable approval records.
Audit evidence
Replay decisions, export bundles, and independently verify what happened after execution.
Connector ecosystem
Apply the same verification model across MCP gateways, engineering systems, enterprise apps, and internal automations.
Latency for production paths
Decision latency is built for real systems, not batch-only governance reviews.
Evidence for security and audit
Every decision can be replayed and every authorized action can be tied back to cryptographic proof.
Rule
No Token, No Action.
The platform is only credible if enforcement is real. Authority Tokens make the boundary enforceable. Audit makes it provable.